We are in the internet generation and are fond of having our data at our fingertips. Since virtualization has simplified our lives, we are also prone to attacks. We really need cybersecurity.
Will you like to miss control over your data?
Will you like to pay ransom for your business?
How does it hear to say that a third party monitors your personal information?
It’s frustating. Isn’t it? But it is what attackers are fond of doing. As we are virtualizing our data, system, and information so that our team and we can access them remotely, we are creating a loophole for the attackers to ping into our privacy.
Whether a single individual or a business holder, you will never like to share your information with any unknown individual. So, you need to know to secure your information, and this can be done by using specified protocols under “Cybersecurity”.
A defining part of Cybersecurity
Cybersecurity is the set of protocols, technologies, processes, and practices to secure our data, systems, programs, networks, and internet transactions from tempering and unauthorized access.
For example, let’s say you are storing your pictures and videos and google drive. Yes, google drive is secure from attackers, but as the data is stored in the cloud, it is penetrable.
There is a possibility that you are sharing your confidential data of business over a messenger application. If it is not end-to-end encrypted, a third party can access your data while transmitting and will use it against you.
So, as you know, what is Cybersecurity? But, which kind of security is lost if an attacker attacks? These security criteria are classified in the “CIA triad”.
Isn’t it interesting to secure ourselves? Explore our CyberSecurity courses for more knowledge.
Build Your Career as a
Cyber Security Specialist
- Live Projects
- Resume / Interview Preparation

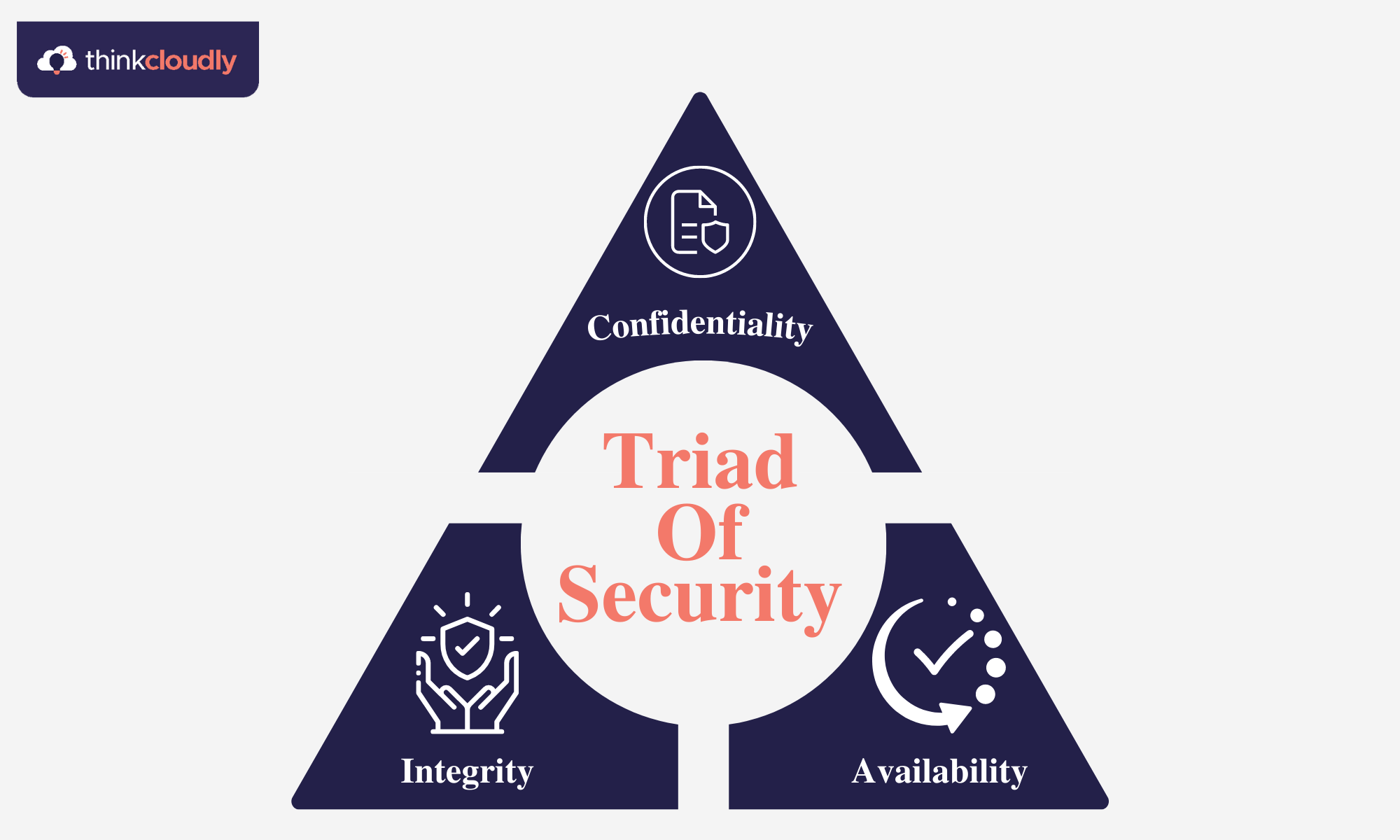
CIA Triad of Security
Security on the internet or in the transmission process is basically of three types, and these are classified as the “CIA triad of Security”. The philosophy in the industry of security is that data is counted to be secure if it is confidential, integrated, and available. If any of these are broken down, then it is a point of concern for the data owner. The words are new to you. Don’t worry. I am here to simplify every misleading term for you.
- Confidentiality: Confidentiality states that any transferred or stored data must be available only to authorized users. It means that there should be restrictions on the disclosure of data to any third party or attackers trying to create a loophole in the system.
- Integrity: Integrity stands out for the security, reliability, and accuracy of data in a system. Integrity states that the data stored in any system is maintained so that it has not been tampered with or changed by any third-party organization or hacker.
- Availability: Availability states that any data should be available to the authorized party. It can be stated as the master of the CIA triad of security as it verifies that the security protocols are called in a manner such that it is nowhere restricting the authorized users.
Boost your earning potential with Cyber Security expertise. Explore our certified Cyber Security courses for a high-paying career
These all are the technical terms of security termed collectively as the CIA triad of security. But what about the regular activities? Cyber attacks are becoming so common that every online device is somehow a suspect of any attacker. So, there are some basic protocols to be followed by every user for their profit of Cybersecurity. We term these protocols “cyber awareness”.
Cyber Awareness
I would like to clearly state that cyber attack is not only things of corporations. Attackers look forward to every individual whose data can benefit them to any extent. If you think corporates are only endangered due to hackers, then you are wrong, my friend.
Every single data of yours can be sold to some authority, and hackers combine the mass data of the public, which can be sold to any authority indulged in miscellaneous bad activities for analytics. Even the hackers can restrict your access to your data and will ask you for ransom for access over your data, and in the end, you will have to pay the demanded ransom. So, cyber awareness is essential.
I have confined the whole concept of cyber awareness to 5 points you must follow at your level to avoid cyber-attacks to an extent.
- Do check your emails properly while clicking over any attached links.
- Don’t grant access to any applications on your devices that seem to be useless. Like, what’s the need for an online video streaming app for your file access? Think about it.
- Please mind the webpage security before downloading any data over the internet.
- Check for the security of any website while granting them access to your emails and other social media profiles. Sometimes a website can ask for access to your Facebook account to proceed and can get access to your profile. So do check about the policies and permissions you are allowing.
- Don’t use third-party applications on your device.
- Gaming and chatting applications are nowadays significant sources of spam. So do check the privacy policies while accessing any of these.
There are many more protocols to follow as cyber attacks can’t be prohibited entirely, nor can rules be confined, but following these can take you towards a path of security to a level.
Points to take back home:
- Cybersecurity is the set of protocols, technologies, processes, and practices to secure our data, systems, programs, networks, and internet transactions from tempering and unauthorized access.
- Security on the internet or in the transmission process is basically of three types, and these are classified as the “CIA triad of Security”.
- Confidentiality states that any transferred or stored data must be available only to authorized users.
- Integrity stands out for the security, reliability, and accuracy of data in a system.
- Availability states that any data should be available to the authorized party.
- Cyber awareness is important at a personal level to keep your life private, not on the internet open to all.
See you in the upcoming blogs. Till then explore more blogs on cybersecurity. Happily Thinkcloudly!